ISO/IEC 27001 Compliant Recycling and Data Destruction
CyberCrunch helps you follow the globally recognized standard for information security management.

Electronics Recycling That Meets International Standards
ISO/IEC 27001 is a global standard for an information security management system (ISMS) that covers data disposal and IT asset recycling. To ensure compliance, companies should choose a data disposal service that securely destroys data beyond recovery.
CyberCrunch adheres to both the Asset Disposal and Information Security Alliance (ADISA) certification and the ISO 27001 standard. We provide a Certificate of Destruction and meet all requirements for secure and responsible IT asset disposal.

The ISO 27001 Requirements for Data and Asset Disposal
To meet ISO 27001 requirements, you must have a regularly reviewed disposal and destruction policy that covers all data and assets. The policy should specify disposal methods and when to use them.
The standard also requires securely erasing data that is no longer needed using appropriate methods for the type of storage media. A disposal and destruction policy should include:
- Defining the scope.
- Records for disposal and destruction.
- An asset register.
- An asset disposal form.
- Assigning responsibilities.
- Selecting appropriate disposal methods.
- Verification of data removal.
At CyberCrunch, we adhere to all the ISO 27001 requirements for secure and compliant data and asset disposal.
CyberCrunch's ISO/IEC 27001 Compliant Data Destruction
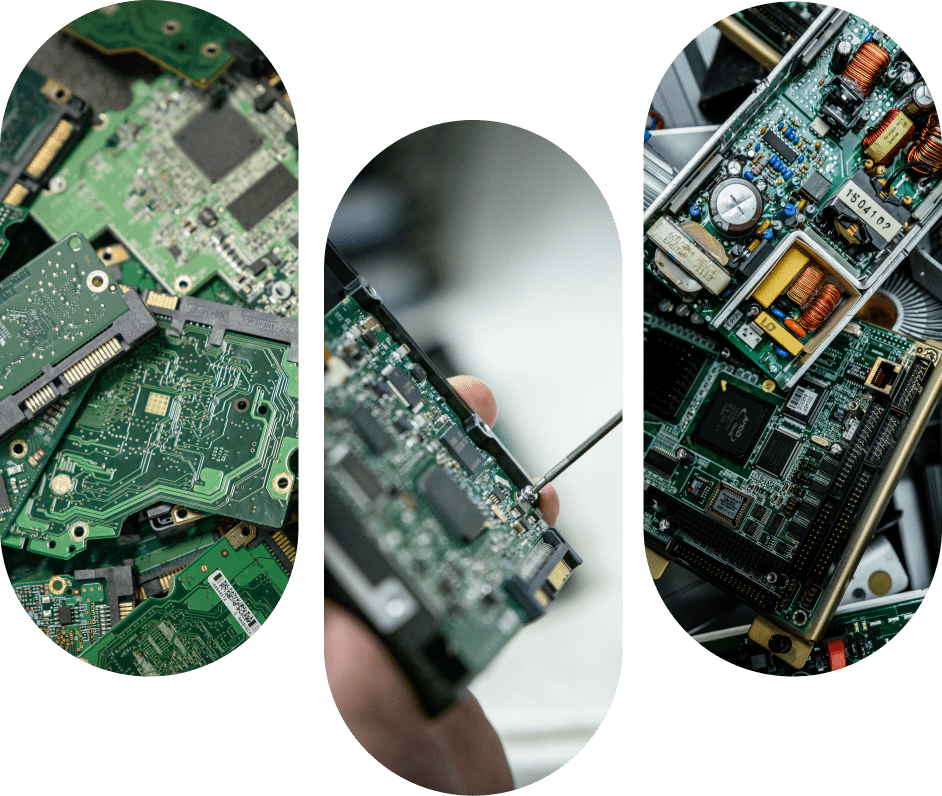
CyberCrunch ensures that all data destruction processes are ISO/IEC 27001 compliant. This means that we have implemented the necessary security controls and processes to protect sensitive information during the disposal process.
We use methods such as degaussing, physical destruction, and secure data wiping for complete and secure data destruction. Our secure facility, where the data destruction takes place, has access controls and surveillance systems in place to prevent unauthorized access.
Protect your organization’s sensitive data by choosing CyberCrunch for ISO/IEC 27001 compliant data destruction services.
Environmental Responsibility
CyberCrunch’s Commitment to Sustainability

CyberCrunch’s processes are designed to minimize waste. We use eco-friendly methods to dispose of electronic waste, such as recycling and repurposing old devices.
Our advanced technology and processes ensure that your data is destroyed in a way that is both secure and environmentally responsible. We reduce your impact on the environment while still handling your data with the utmost care.
Trust CyberCrunch to responsibly dispose of your IT assets and meet your ISO/IEC 27001 data security needs.
Recycling & Destruction Service Process
Safe, Secure, and Simple IT Equipment Disposal
Online Pickup Scheduling
Secure Global Recycling Logistics
Data Destruction
Proof of Compliance
"Easy to schedule pickup. The guys that came to pick up equipment were nice and picked up all containers along with a few heavier items that we couldn’t get into the container. The company provided tracking for trucks and arrived when promised. Everything handled professionally."
"Great service. Scheduled online and you were here the next day. Thanks again!"
— David
Manager
"Thanks for helping us set up the disposal this morning, The guys that came were great and we got everything removed!"
— Brittany
Sustainability Manager
"The materials were picked up. Service from driver was excellent. I know you will send an invoice. I look forward to working with you again."
— Paul
Analyst
"I just wanted to let you know that Gary was wonderful to work with today! He’s such a professional – he made this super easy for us!"
CyberCrunch is trusted by 250+ leading companies




Protect Your Enterprise from Data Breaches
Cyber threats are on the rise.
Our secure IT asset disposal services help you safeguard sensitive corporate data, mitigate risks, and maintain compliance.
Compliance & Certifications
At CyberCrunch, we take compliance and certifications seriously. We are certified in the following areas to provide you with peace of mind when it comes to disposing of your business’s electronics:
HIPAA Compliance
Protecting sensitive patient data in the healthcare industry.
PCI Compliance
Complying with the Payment Card Industry Data Security Standard (PCI DSS) to protect your business's credit card data.
GDPR Compliance
Complying with the General Data Protection Regulation (GDPR) to protect individuals' privacy rights.
R2 Certified Recycling**
Adhering to the highest standards of responsible electronics recycling.
NAID-AAA Data Destruction**
Following strict protocols for data destruction to protect your business's sensitive information.
We also offer cyber insurance that fully covers the electronic recycling process, from pickup to final disposal.
**CyberCrunch Greensburg, PA facility is certified to R2V3, RIOS, & NAID-AAA